About Cyber Security Course
Cyber threats have expanded in type and scale with the advent of digitization, both at the company level as well as at that of governments and individuals. Unsurprisingly, the demand for skilled cybersecurity professionals is greater than ever. In a city like Kolhapur, which is growing technologically at a fast pace, learning would be mandatory. To fill this rising demand, the Cyber Security Course in Kolhapur has been designed to provide students, IT professionals, and corporations with advanced knowledge of cybersecurity as well as problem-solving skills.
These programs offer practical training where the students learn to work in real-life scenarios such as threat detection, network security, penetration testing, and cryptography, among others. Students gain technical knowledge as well as strong skills in risk assessment, incident response, and security policy compliance. The course curriculum usually follows industry standards such as ISO/IEC 27001 and the NIST framework, ensuring students learn international best practices.
Understanding the Scope of Cybersecurity
No longer is cybersecurity an IT specialty; it is a fundamental element of every modern Business. Defending individual nodes and networks through to securing critical infrastructures and cloud-based systems, cybersecurity encompasses a number of domains. Cyberattackers are more sophisticated now and leverage AI, social engineering, and zero-day vulnerabilities to infiltrate systems. That means responding in cybersecurity is not sufficient; now organizations require a proactive and preventative approach, which can only be planned and executed with a skilled person.
The cybersecurity course in Kolhapur is designed to provide a deep insight into the most recent techniques of network safety, application security, endpoint protection, identity and access management , along with vulnerability evaluation. Utilizing live equipment such as tablets, Windows OS machines, and VLANs – with real-world simulations and tools like Wireshark, the Metasploit penetration testing software, Kali Linux, which is a custom distribution used for Penetration Testing , Nessus vulnerability scanner software- students experience industry-relevant hands-on lab exercises that give them a practical understanding of these critical systems.
Curriculum Focus and Industry-Relevant Modules
Cyber Security Courses in Kolhapur offered by SevenMentor follow the latest syllabus, which change according to time to time as updates come from the cyber world. It includes the key topics from firewalls, intrusion detection systems, and VPNs to advanced topics like hacking, reverse engineering, malware analysis, and digital forensics. Join the top Cyber Security Course in Kolhapur to learn ethical hacking and network defence. Launch your career with a pro-led Cyber Security Course in Kolhapur now!
Training modules are purposefully constructed to be a balanced Red (offensive) Team / Blue (defensive) Team model. For example, students delve into Red Team skills such as penetration testing, ethical hacking labs, and ‘capture the flag’ simulated attack games; and Blue Team modules cover threat prevention, SIEM (Security Information and Event Management), and forensic investigation programmes. Every concept is backed with hands-on exposure, such as corpora and scenario-based assessment for a hunt experience into the real world.
The Best Cyber Security training institute differs from other generic providers that you find on the internet because of its based practices and decades of professional experience with real data protection.
Certifications and Career Pathways
After training, students typically seek IT security certifications such as CompTIA Security+, Certified Ethical Hacker (CEH), CISSP, or CISM. These certifications contribute extensively to your professional image and are actually yardsticks in the recruitment game.
After getting the Cyber Security Classes in Kolhapur, professionals may check job trends as Security Analyst, Penetration Tester, Security Consultant, SOC Analyst, and Security Architect. They range from IT companies to banks, manufacturing plants, health systems, and government organizations, all of whom are facing cybersecurity challenges that must be addressed by professionals.
Specialists who possess the skills to secure DevOps pipelines, cloud environments (e.g., AWS, Azure), and IoT networks are much in demand as well. The topography of the course RTT
Lab Infrastructure and Project-Based Learning
The real-life, Project-based approach is the cornerstone of Cyber Security Training in Kolhapur at SevenMentor. "Lab sessions contain sandboxes that are the same as enterprise security architectures." Trainees are provided access to virtual machines implementing insecure applications to attack and defend. Every student is engaged in capstone activities, such as hardening a network or designing a security operations center (SOC), or conducting a vulnerability assessment on an enterprise system emulation.
These aren’t just academic projects—they are catered to industry expectations and revised by computer security professionals who work in the field. Through interactive work, participants are made to appreciate why and not just how security measures are implemented. This hands-on approach works to ensure that every person taking part knows exactly what they are doing whenever it comes to security.
Faculty Expertise and Mentorship
The faculty is the heart of any training program. At SevenMentor Best Cyber Security Training Institute, Our Trainers are certified and have general security expertise along with relevant industry experiences, with penetration testing on the side, and secure operations. Experience One of the best in the business Working on live security incidents Red teaming engagements Cybercrime investigation This is real-life experience that translates into mentorship beyond the pages of a textbook.
In addition, mentors assist learners in constructing a professional portfolio by providing guidance on publishing security research, hunting bug bounties, and participating in Capture The Flag (CTF) competitions. These after-school activities also help to improve the learning outcomes and specialization of our students in global cybersecurity careers.
Placement Support and Industry Collaboration
One of the key features of Cyber Security training in Kolhapur is that they provide job placement support. From resume creation to preparing for interviews, mock assessments, and company tie-ups refers to nice Cyber Security Training Institutes like SevenMentor. You get everything in the form of support. They also have relationships with top security companies, IT consultancies, and start-ups, which often recruit talented individuals for different positions.
Employers in particular favor candidates trained in both theoretical and technical aspects of cybersecurity, such as those who can work with SIEM tools like Splunk, QRadar, or LogRhythm, and understand regulatory compliance, including GDPR, HIPAA, and PCI DSS.
WHY Opt Cyber Security COURSE FROM KOLHAPUR?
It is the ride to Kolhapur, which seems to be emerging as a Tech city with several businesses setting up shop of their digital operations. That sets a good base for budding cybersecurity professionals to train and work without having to move into big metro cities. Kolhapur's education ecosystem is bolstered by the presence of colleges and startup incubators, professional training centers, and talent acquisition and skill development.
In addition, the area has ample infrastructural support, mentorship, and a learning community that values its students. This is where people network, connect, and learn from one another in the industry.
In an era where data is the driving force behind every operation, cybersecurity has emerged as a basic requirement for everyone. The threat landscape is broadening, and a new breed of cybercrime response professionals needs to understand the threats and manage their response effectively, both armed with an understanding of their capabilities. Our Cyber Security Classes in Kolhapur fill this skills-gap by providing high-quality training and innovative courses that are academically challenging and relevant to the industry.
Online Cyber Security Training
Online Cyber Security Courses in Kolhapur. SevenMentor provides the best online training for Cyber Security. The Kolhapur Cyber Security online training program is designed to replicate the in-class feeling of sitting with the instructor, even though you are halfway across the world. Labs are available to all participants via cloud-based solutions, providing the same practical and hands-on learning experience in a virtual environment.
Best Online Cyber Security Classes in Kolhapur is also known as Isara Solutions online development classes Which allows Working Professionals, College students, or Individuals Outside Kolhapur to get access to quality training without relocation. Furthermore, all classes are recorded to create learning reference materials for students, which can be used to review difficult topics and help improve understanding at one's own pace.
Corporate Cyber Security Course
SevenMentor also provides the corporate Cyber Security Course in Kolhapur. They are customized to the organization and can be offered on-site or remotely. Subjects are tailored to meet business requirements, and include endpoint security, phishing defense, compliance management, and SOC team enablement.
For corporate clients, post-training assessments and employee performance reports are included to measure the impact of the learning intervention. That makes corporate cybersecurity training more than a defensive play — it’s a strategic investment in operational resiliency.
 A comprehensive cybersecurity strategy has numerous layers of protection.
A comprehensive cybersecurity strategy has numerous layers of protection.  Prevention of cyber attacks is the primary goal of a Cyber expert.
Prevention of cyber attacks is the primary goal of a Cyber expert. An organization's people, processes, and technology must complement one another to effectively defend against cyber threats.
An organization's people, processes, and technology must complement one another to effectively defend against cyber threats.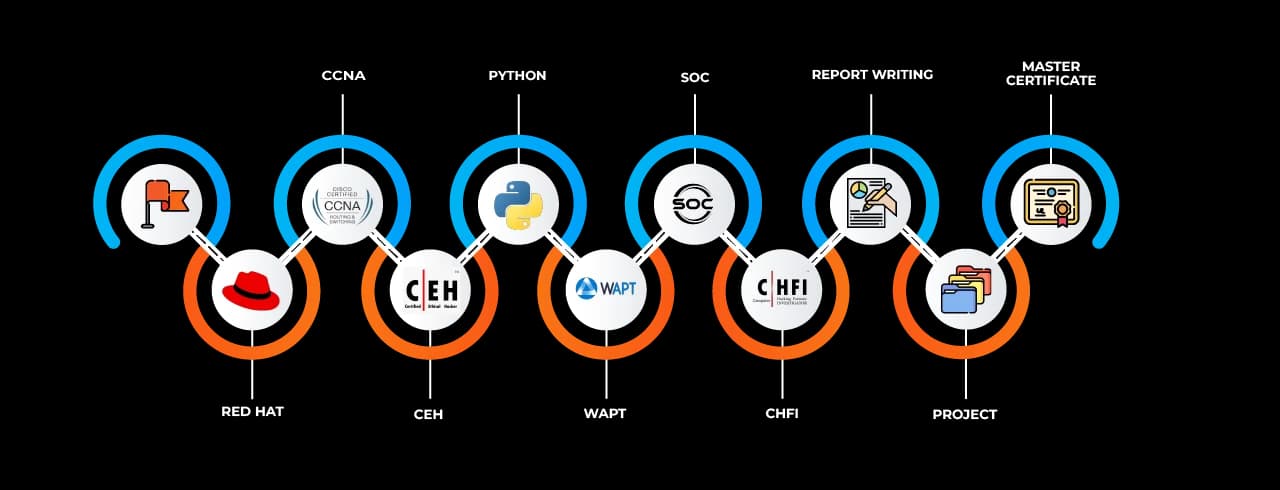


-1744728435835.webp&w=3840&q=75)



